Use CLI for Microsoft to get HaveIBeenPwned status
When we released the latest version of the CLI for Microsoft 365 we were able to finally push in in our m365 aad user hibp command. This allows you to check if there are Have I Been Pwned reports for a specific account. A great reason to build a new quick sample script 🚀.
Have I been Pwned
The ’;–have i been pwned? site is a well known site allowing you to check if your e-mail or phone number is part of a known data breach. Without going into the details it is a pretty handy tool to check for data breaches.
The most common use of the API provided is to return a list of all breaches a particular account has been involved in. So now that we have support in the CLI for Microsoft 365 you can combine this insight into your other reports.
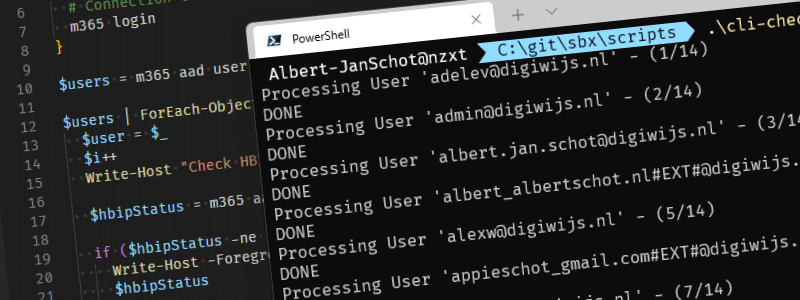
In our sample we want to retrieve all accounts on our dev tenant and check against known data breaches. The current implementation does not check against pastes but only breaches!.
So with other samples already available this one is pretty straight forward:
- Get all users
- Run the Have I Been Pwned command against those
- Write out issues if a user is part of breach
No other logic required except that you need an API key that will set you back $3,50.
$m365Status = m365 status
$apiKey = "XXXXXX"
if ($m365Status -eq "Logged Out") {
# Connection to Microsoft 365
m365 login
}
$users = m365 aad user list --properties "displayName,userPrincipalName" | ConvertFrom-Json
$users | ForEach-Object {
$user = $_
$i++
Write-Host "Check HBIP status for user '$($user.userPrincipalName)' - ($i/$($users.length))"
$hbipStatus = m365 aad user hibp --userName $user.userPrincipalName --apiKey $apiKey --verbose | ConvertFrom-Json
if ($hbipStatus -ne "No pwnage found") {
Write-Host -ForegroundColor Red "Issue with user '$($user.userPrincipalName)'"
$hbipStatus
}
Start-Sleep -Milliseconds 1500
}
A final remark is that the API is rate limited. Any requests to the breaches and pastes APIs are limited to one per every 1500 milliseconds, so a Start-Sleep is added to prevent rate limiting to kick in! Now for this sample no other actions are executed for accounts breached; but you could argue that those accounts should be notified. For instance by sending an e-mail with m365 outlook mail send or planning an action for further investigation.